Astro’s transformation with sooka
Powered by Irdeto Experience to lead in streaming
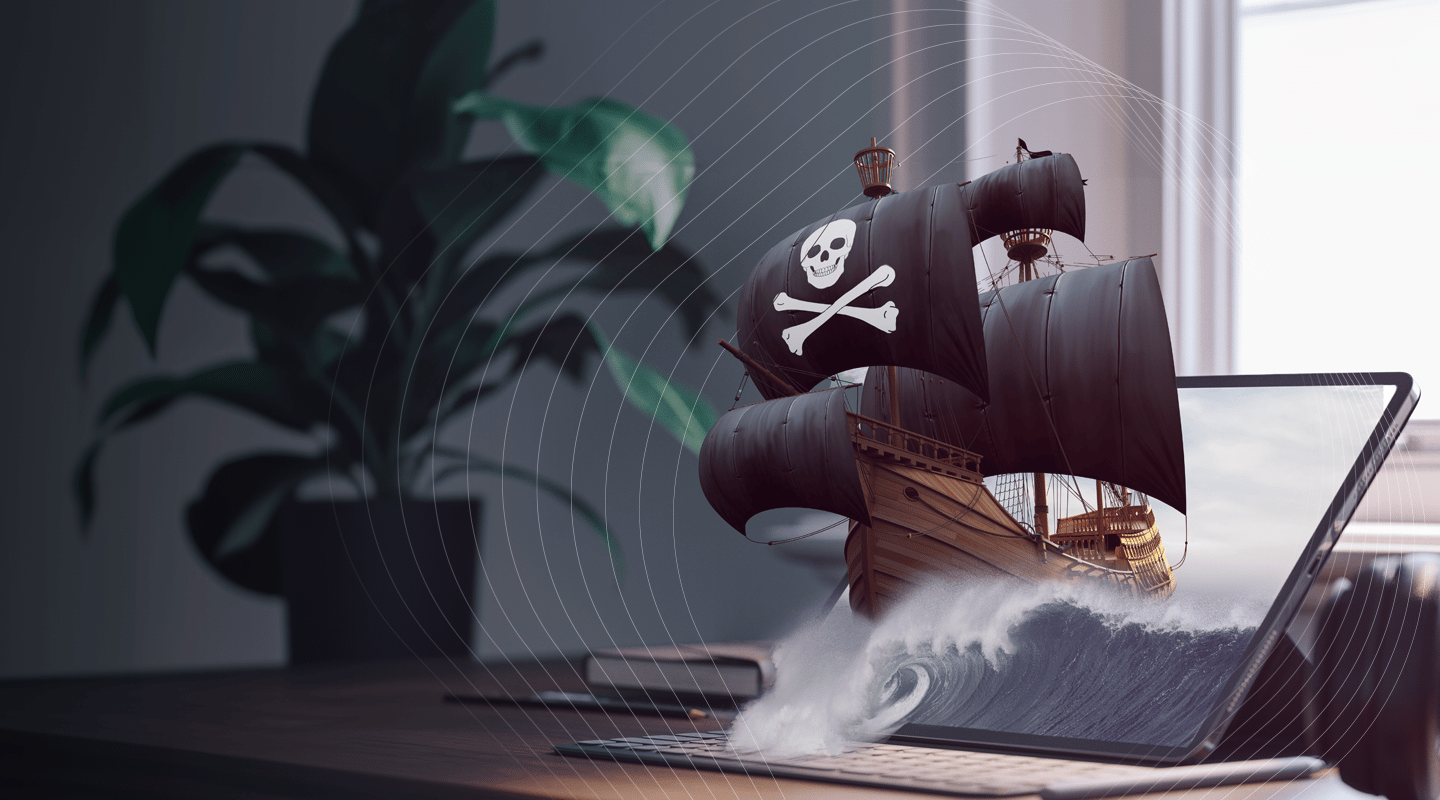
Complete coverage against video piracy
Comprehensive protection
- Ensure end-to-end security across your services
- Protect your content, brand and investments
- Reduce revenue loss from piracy
- Stay compliant with content licensing requirements
- Build and maintain viewer trust
Agile detection and enforcement
- Execute proactive detection of piracy threats
- Get swift analysis of infringement instances
- Disrupt payment channels used by pirates
- Take targeted enforcement and takedown actions
- Respond fast to shut down piracy

Integrated technology and human intelligence
- Track misuse with forensic watermarking
- Detect threats through proactive monitoring
- Address issues with local investigators
- Enforce rights via global partnerships
- Strengthen protection with tech and experts
Real-world successes from our anti-piracy efforts
71%
decrease in pirated IPTV and credential ads
25%
reduction in CDN costs caused by piracy and abuse
93%
drop in pirate site traffic via payment disruption
Protecting sports revenue, preserving the passion
Explore success stories where premium video providers, with Irdeto’s expertise, fought piracy and secured content, revenue and fan engagement, keeping sports thriving worldwide.
Disrupting piracy at scale
Learn how SuperSport tackled large-scale piracy, protected premium sports rights and secured revenue with a multi-layered, real-time defense strategy.

Stopping leaks before they spread
See how a global media company detects and stops pre-release leaks early, protecting high-value content, launch integrity and audience experience.

Winner of “2024 Best Anti-Piracy Solution”
Our 5-step program for E2E anti-piracy and cybersecurity management











/Images/Module%20-%20footer/spiral.svg)
