
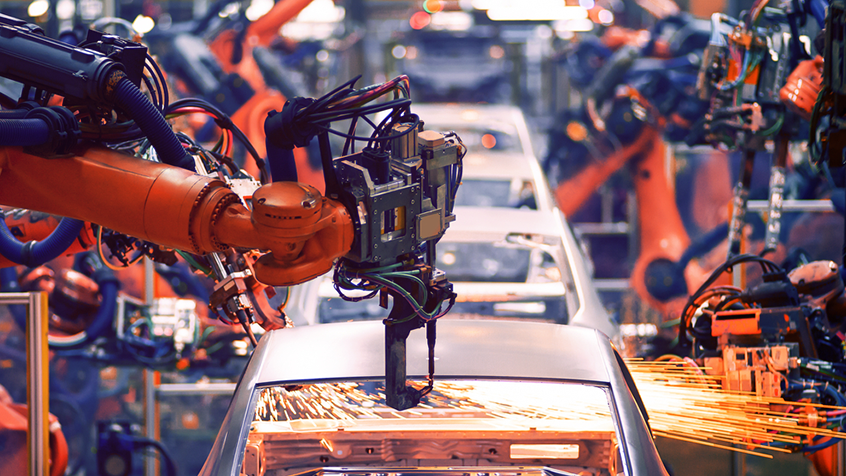
Smart mobility solutions
Powering smarter, safer and more efficient access across fleets, automotive OEMs and EV charging
Partnered with:
Irdeto, Hubject and Gireve partnership
Expanding global Plug & Charge access
Simple, secure, scalable growth for smart mobility
A new era of mobility
Mobility is evolving fast, but fragmented systems, manual processes, security risks and poor interoperability are slowing scale, efficiency and innovation across fleets, automotive OEMs and EV charging.

Security that drives revenue
Irdeto combines decades of security expertise with mobility insight. With Keystone and Irdeto CrossCharge, we securely simplify operations, enable interoperability, and drive monetization across the smart mobility industry.

Proven, trusted, ready to scale
Trusted by OEMs, fleets and operators worldwide, Irdeto secures over 2 billion keys. Our open, standards-based solutions deploy fast, scale easily and deliver strong ROI, while enabling freedom to integrate with any ecosystem.

Who do we serve?
We help mobility innovators secure access, simplify operations and scale with trusted solutions

Digital fleet access
- Heavy-duty trucking fleets
- Last mile delivery operators
- Vehicle rental and leasing providers
- LTL and regional carriers
- Fleet telematics and OEM integration partners
Automotive OEM digital key
- Passenger vehicles
- Light commercial vehicles
- Heavy commercial vehicles

EV charging
- eMobility service providers
- EV manufacturers
- Charge point operators
- Electric fleet operators
- EV charging manufacturers
Secure by design, open and built for growth
Unlock efficiency, interoperability and control across fleets, EV charging and passenger vehicles

Keystone by Irdeto
Replaces physical keys with secure digital access for heavy-duty and light-duty fleets. It streamlines operations, reduces key-related delays and cuts labor costs. With centralized control, real-time tracking and fast deployment, Keystone improves accountability, enhances security and delivers measurable ROI for fleets managing complex access across vehicles and drivers.

Irdeto CrossCharge
Enables seamless, secure Plug & Charge across EVs, chargers, and networks, no lock-in. Built on open standards, it supports OEMs, CPOs, eMSPs and fleets with scalable infrastructure, strong data protection and regulatory compliance. Businesses gain flexibility, lower costs and full ecosystem interoperability to grow their electric mobility footprint with confidence.

Awards and recognition
/Images/Module%20-%20footer/spiral.svg)
